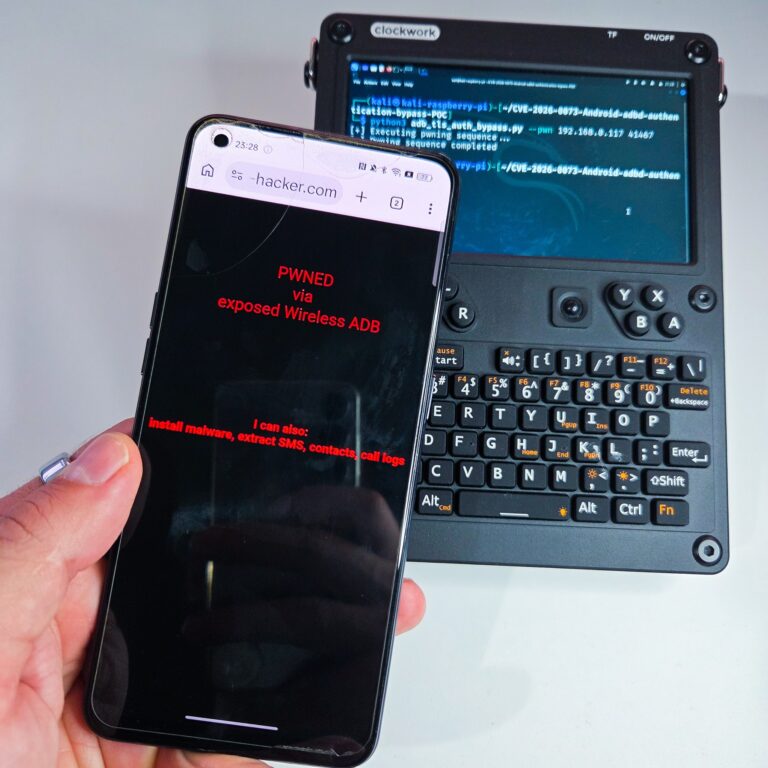
In May 2026, Google disclosed CVE‑2026‑0073 as a Critical vulnerability in the Android System component, specifically the adbd subcomponent (part of the ADB stack). The bulletin states it could lead to remote (proximal) code execution as the shell user with no user interaction required.