Pi‑hole on Android: Turn Your Spare Smartphone into a Network‑Wide Ad‑Blocker
In this blog, I’ll walk you through: What Pi‑hole is and how DNS sinkholes work. Typical Pi‑hole deployments (e.g., Raspberry...

![]()
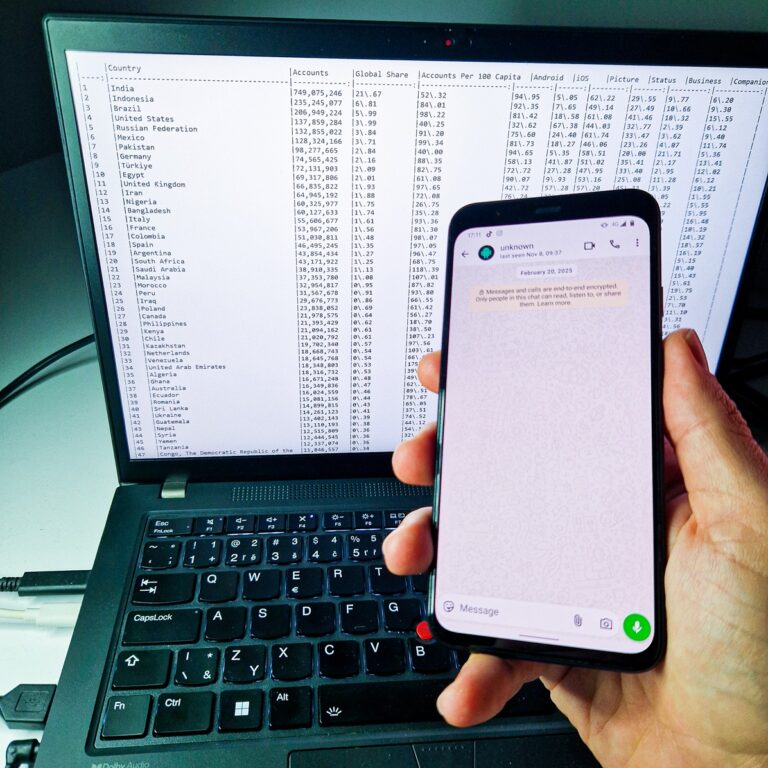
The dataset originates from metadata published in connection with a security study titled “Trivial WhatsApp Security Issue Exposed 3.5 Billion Phone Numbers.” That research demonstrated how a simple flaw could reveal phone numbers globally.
![]()
It’s not perfect, but it works—a clever DIY project that blends portability, privacy, and practicality.


![]()
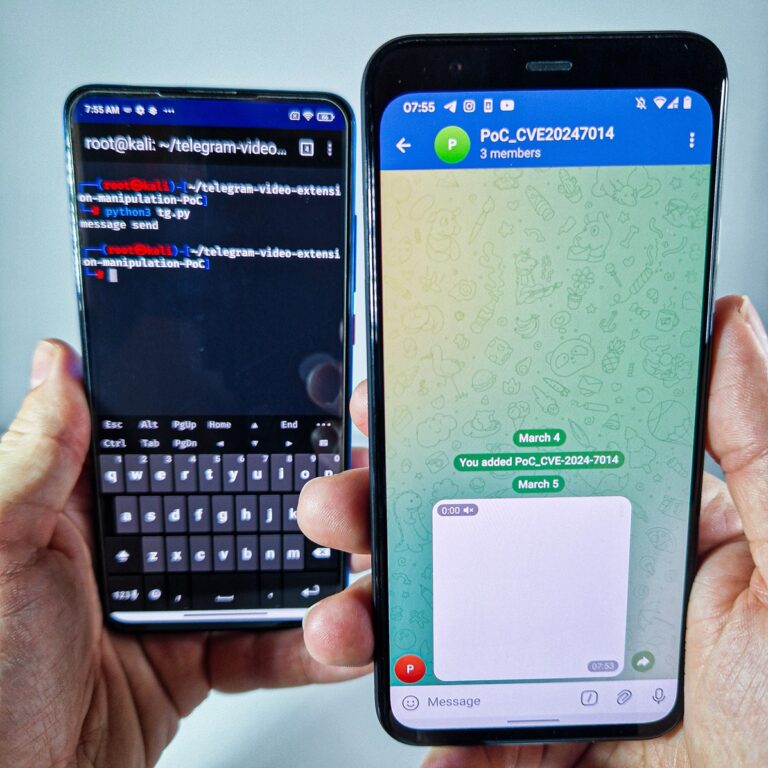
A newly disclosed in Telegram for Android, dubbed EvilLoader, allows attackers to disguise malicious APKs as video files, potentially leading to unauthorized malware installations on users’ devices.